05
фев
05
фев

Setup Kerberos Install MIT Kerberos. On Ubuntu the package manager can install this: sudo apt-get install krb5-user The dependencies for this package will provide the rest of the required files. Edit /etc/krb5.conf [libdefaults] default_realm = ACME.LOCAL [domain_realm] acme.local = ACME.LOCAL [realms] ACME.LOCAL = { kdc = win2k3.acme.local admin_server = win2k3.acme.local Test your Kerberos configuration so far: • Ensure that you can ping between the Windows 2003 server and the linux server in both directions and using both the fully-qualified domain name (win2k3.acme.local) and the IP address.
Note: You must be able to ping your Windows 2003 KDC using the fully-qualified domain name from the linux host. In the unlikely event you have mDNS enabled this will fail if your Active Directory domain ends in.local.
Feb 26, 2017 - 1 Basic LDAP authentication; 2 Apache single sign-on. Found in similar documentation elsewhere for tools expecting to work against a Windows AD. You will need to install the libapache2-mod-auth-kerb package (Debian).
If you try to work around the name resolution issue by entering the IP address in krb5.conf, the next test will succeed but Apache authentication will fail later with 'No principal in keytab matches desired name' in the Apache error log. • In a shell type kinit.LOCAL, entering an Active Directory username you know. If it is successful it will ask for the account's password and then exit without an error. Use klist to view the Kerberos ticket that was just added to the machine. Setting up a keytab file Now switch to your Windows 2003 server and create a user account that will represent the HTTP service on the linux server.
Passazhirskie vagoni dlya trainz 2012 free. • Satellite View - Zoom all the way out and view your railroad from satellite distance • More realistic trees with new SpeedTree Assets • Backward compatible with Trainz Simulator 2010 content • Southern China • ECML Kings Cross - Newcastle • Balezino - Mosti • Debrecen - Nyiregyhaza • Mojave Sub Division • Municipal transit railway • Norfolk & Western - Appalachian Coal • Northeast Corridor - Wilmington To Philadelphia • New in-game downloadable content system for both payware and freeware options. • An expanded sound library. • New in-game navigation system with a HUD UI.
Let's use wikikerb. We will use ktpass from the Windows 2003 Support Kit to create a keytab file the linux server will need. At the command line, enter ktpass /out c: my.keytab /mapuser HTTP-user@acme.local /princ HTTP/wikisvr.acme.local@ACME.LOCAL /crypto RC4-HMAC-NT /pass passw0rd /ptype KRB5_NT_PRINCIPAL Note: Even if you created a CNAME to redirect wiki.acme.com to wikisvr.acme.local, and all your users will be entering wiki.acme.com, the principal name ( -princ) must still use the canonical DNS name. This will not affect what your users need to type to get to the site.
Copy the keytab file to the linux server and place it in /etc/apache2. Test the keytab file like so: kinit -k -t /etc/apache2/http.keytab HTTP/wikisvr.acme.local This should exit without any error messages, and this Kerberos ticket will now appear in klist. If you want to purge the ticket cache use kdestroy. Alternatively, instead of using kinit, proceed to configuring mod_auth_kerb for Apache. For more information see the guide at.
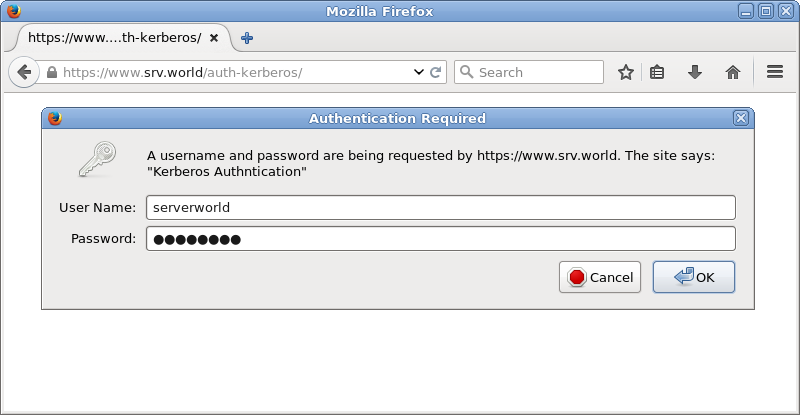
Setup mod-auth-kerb Once again the package manager works wonders: sudo apt-get install libapache2-mod-auth-kerb In /etc/apache2/conf.d/twiki.conf, add the entries for Kerberos authentication. Enter # in front of AuthType basic to disable plain text authentication.
Order Deny, Allow Allow from all AuthType Kerberos KrbAuthRealms ACME.LOCAL KrbServiceName HTTP Krb5Keytab /etc/apache2/http.keytab KrbMethodNegotiate on KrbMethodK5Passwd on Require valid-user. NewUserPlugin The works great with this setup, and creates the user page when they first login by copying a template and filling in their details from LDAP. -- Contributor:, - 05 Dec 2009-12-28 Comments & Questions about this Supplemental Document Topic Thanks Matt for contributing this topic. I moved it from the Main web, linked to it from and tagged it so people can discover it. -- - 07 Dec 2007 Excellent! I am using a similar setup, but have to apologize that I was too lazy to write it down. I am curious about how you are using to create wikinames.

Setup Kerberos Install MIT Kerberos. On Ubuntu the package manager can install this: sudo apt-get install krb5-user The dependencies for this package will provide the rest of the required files. Edit /etc/krb5.conf [libdefaults] default_realm = ACME.LOCAL [domain_realm] acme.local = ACME.LOCAL [realms] ACME.LOCAL = { kdc = win2k3.acme.local admin_server = win2k3.acme.local Test your Kerberos configuration so far: • Ensure that you can ping between the Windows 2003 server and the linux server in both directions and using both the fully-qualified domain name (win2k3.acme.local) and the IP address.
Note: You must be able to ping your Windows 2003 KDC using the fully-qualified domain name from the linux host. In the unlikely event you have mDNS enabled this will fail if your Active Directory domain ends in.local.

Feb 26, 2017 - 1 Basic LDAP authentication; 2 Apache single sign-on. Found in similar documentation elsewhere for tools expecting to work against a Windows AD. You will need to install the libapache2-mod-auth-kerb package (Debian).
If you try to work around the name resolution issue by entering the IP address in krb5.conf, the next test will succeed but Apache authentication will fail later with \'No principal in keytab matches desired name\' in the Apache error log. • In a shell type kinit.LOCAL, entering an Active Directory username you know. If it is successful it will ask for the account\'s password and then exit without an error. Use klist to view the Kerberos ticket that was just added to the machine. Setting up a keytab file Now switch to your Windows 2003 server and create a user account that will represent the HTTP service on the linux server.
Passazhirskie vagoni dlya trainz 2012 free. • Satellite View - Zoom all the way out and view your railroad from satellite distance • More realistic trees with new SpeedTree Assets • Backward compatible with Trainz Simulator 2010 content • Southern China • ECML Kings Cross - Newcastle • Balezino - Mosti • Debrecen - Nyiregyhaza • Mojave Sub Division • Municipal transit railway • Norfolk & Western - Appalachian Coal • Northeast Corridor - Wilmington To Philadelphia • New in-game downloadable content system for both payware and freeware options. • An expanded sound library. • New in-game navigation system with a HUD UI.
Let\'s use wikikerb. We will use ktpass from the Windows 2003 Support Kit to create a keytab file the linux server will need. At the command line, enter ktpass /out c: my.keytab /mapuser HTTP-user@acme.local /princ HTTP/wikisvr.acme.local@ACME.LOCAL /crypto RC4-HMAC-NT /pass passw0rd /ptype KRB5_NT_PRINCIPAL Note: Even if you created a CNAME to redirect wiki.acme.com to wikisvr.acme.local, and all your users will be entering wiki.acme.com, the principal name ( -princ) must still use the canonical DNS name. This will not affect what your users need to type to get to the site.
Copy the keytab file to the linux server and place it in /etc/apache2. Test the keytab file like so: kinit -k -t /etc/apache2/http.keytab HTTP/wikisvr.acme.local This should exit without any error messages, and this Kerberos ticket will now appear in klist. If you want to purge the ticket cache use kdestroy. Alternatively, instead of using kinit, proceed to configuring mod_auth_kerb for Apache. For more information see the guide at.
Setup mod-auth-kerb Once again the package manager works wonders: sudo apt-get install libapache2-mod-auth-kerb In /etc/apache2/conf.d/twiki.conf, add the entries for Kerberos authentication. Enter # in front of AuthType basic to disable plain text authentication.
Order Deny, Allow Allow from all AuthType Kerberos KrbAuthRealms ACME.LOCAL KrbServiceName HTTP Krb5Keytab /etc/apache2/http.keytab KrbMethodNegotiate on KrbMethodK5Passwd on Require valid-user. NewUserPlugin The works great with this setup, and creates the user page when they first login by copying a template and filling in their details from LDAP. -- Contributor:, - 05 Dec 2009-12-28 Comments & Questions about this Supplemental Document Topic Thanks Matt for contributing this topic. I moved it from the Main web, linked to it from and tagged it so people can discover it. -- - 07 Dec 2007 Excellent! I am using a similar setup, but have to apologize that I was too lazy to write it down. I am curious about how you are using to create wikinames.
...'>How To Install Modauthkerb For Windows(05.02.2019)
Setup Kerberos Install MIT Kerberos. On Ubuntu the package manager can install this: sudo apt-get install krb5-user The dependencies for this package will provide the rest of the required files. Edit /etc/krb5.conf [libdefaults] default_realm = ACME.LOCAL [domain_realm] acme.local = ACME.LOCAL [realms] ACME.LOCAL = { kdc = win2k3.acme.local admin_server = win2k3.acme.local Test your Kerberos configuration so far: • Ensure that you can ping between the Windows 2003 server and the linux server in both directions and using both the fully-qualified domain name (win2k3.acme.local) and the IP address.
Note: You must be able to ping your Windows 2003 KDC using the fully-qualified domain name from the linux host. In the unlikely event you have mDNS enabled this will fail if your Active Directory domain ends in.local.

Feb 26, 2017 - 1 Basic LDAP authentication; 2 Apache single sign-on. Found in similar documentation elsewhere for tools expecting to work against a Windows AD. You will need to install the libapache2-mod-auth-kerb package (Debian).
If you try to work around the name resolution issue by entering the IP address in krb5.conf, the next test will succeed but Apache authentication will fail later with \'No principal in keytab matches desired name\' in the Apache error log. • In a shell type kinit.LOCAL, entering an Active Directory username you know. If it is successful it will ask for the account\'s password and then exit without an error. Use klist to view the Kerberos ticket that was just added to the machine. Setting up a keytab file Now switch to your Windows 2003 server and create a user account that will represent the HTTP service on the linux server.
Passazhirskie vagoni dlya trainz 2012 free. • Satellite View - Zoom all the way out and view your railroad from satellite distance • More realistic trees with new SpeedTree Assets • Backward compatible with Trainz Simulator 2010 content • Southern China • ECML Kings Cross - Newcastle • Balezino - Mosti • Debrecen - Nyiregyhaza • Mojave Sub Division • Municipal transit railway • Norfolk & Western - Appalachian Coal • Northeast Corridor - Wilmington To Philadelphia • New in-game downloadable content system for both payware and freeware options. • An expanded sound library. • New in-game navigation system with a HUD UI.
Let\'s use wikikerb. We will use ktpass from the Windows 2003 Support Kit to create a keytab file the linux server will need. At the command line, enter ktpass /out c: my.keytab /mapuser HTTP-user@acme.local /princ HTTP/wikisvr.acme.local@ACME.LOCAL /crypto RC4-HMAC-NT /pass passw0rd /ptype KRB5_NT_PRINCIPAL Note: Even if you created a CNAME to redirect wiki.acme.com to wikisvr.acme.local, and all your users will be entering wiki.acme.com, the principal name ( -princ) must still use the canonical DNS name. This will not affect what your users need to type to get to the site.
Copy the keytab file to the linux server and place it in /etc/apache2. Test the keytab file like so: kinit -k -t /etc/apache2/http.keytab HTTP/wikisvr.acme.local This should exit without any error messages, and this Kerberos ticket will now appear in klist. If you want to purge the ticket cache use kdestroy. Alternatively, instead of using kinit, proceed to configuring mod_auth_kerb for Apache. For more information see the guide at.
Setup mod-auth-kerb Once again the package manager works wonders: sudo apt-get install libapache2-mod-auth-kerb In /etc/apache2/conf.d/twiki.conf, add the entries for Kerberos authentication. Enter # in front of AuthType basic to disable plain text authentication.
Order Deny, Allow Allow from all AuthType Kerberos KrbAuthRealms ACME.LOCAL KrbServiceName HTTP Krb5Keytab /etc/apache2/http.keytab KrbMethodNegotiate on KrbMethodK5Passwd on Require valid-user. NewUserPlugin The works great with this setup, and creates the user page when they first login by copying a template and filling in their details from LDAP. -- Contributor:, - 05 Dec 2009-12-28 Comments & Questions about this Supplemental Document Topic Thanks Matt for contributing this topic. I moved it from the Main web, linked to it from and tagged it so people can discover it. -- - 07 Dec 2007 Excellent! I am using a similar setup, but have to apologize that I was too lazy to write it down. I am curious about how you are using to create wikinames.
...'>How To Install Modauthkerb For Windows(05.02.2019)